Hardened mobile
Trusting the computer that follows you around all day
2015-02-15 — 2021-08-06
Wherein the mobile twin to hardened desktops is examined; methods for reducing phone spyware via accountability are outlined, hardware options like Librem 5 and Precursor are surveyed, and on‑device CSAM scanning is noted.
Suspiciously similar content
The mobile twin to hardened desktop OSes.
Reducing the amount of spyware on your phone through better accountability.
(Securing the apps is a whole ’nother layer atop that.)
Side question: How secure are minimal environments like KaiOS?
Tracking market prices for vulnerabilities is one option for evaluating risk.
1 iOS
iOS is a barometer. iOS seemed to be somewhat secure, but has thrown that cred out by including automated child sexual abuse image scanning for the police. As with many things, the feature is justified by peds-under-the-bed rhetoric. Antonio García Martínez opines this is a least-harm option in Hunting predators. What exactly is the threat model?
2 Basic Android securing
Which Android phones do not leave gaping unpatched security holes?. *tl;dr — Google, LG, then everyone else.
- 🏗 Google tracking Android devices
The hypothetical grugq phone is a hardened Android variant.
Is LineageOS Android Distribution easier to secure? It is at least less corporate-spyware-ey.
3 Open-ish hardware: Librem
An alternative route is the Purism Librem 5. Their product seems less to be a phone than a little Linux laptop which happens to be a phone. It runs a hardened Debian variant PureOS which is a full desktop OS. Essentially this means you get all the resources and tools of the Open Source community’s auditing and development, and also all the horror of the Open Source community’s terrible UX track record, wrapped up in one device of unspecified battery life. It looks kind of fun, in a stubborn hobbyist kind of way. I wonder how secure this phone truly is on hostile networks. For sure its configuration is screamingly weird enough that generic attacks are unlikely to work.
4 Ultra-open auditable hardware
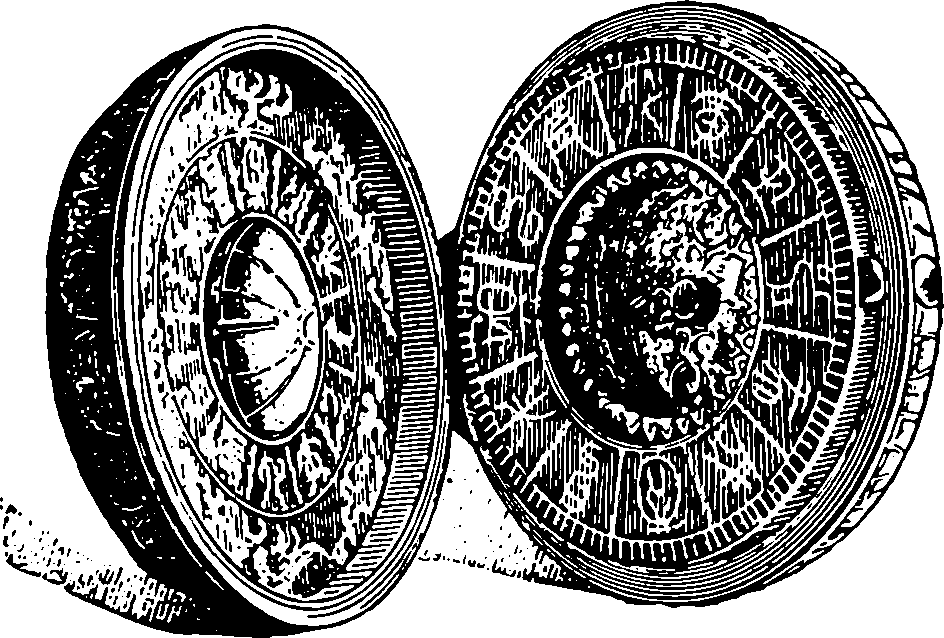
Precursor is a trusted-computing mobile device with endorsement by Bunnie Huang. It has an intriguing introduction to trustable hardware.
5 App selection
It is not clear which apps are safe. For example, Tiktok is not.
The same fingerprinting script and cookie is used on Bytedance’s news site Toutiao. So: If someone shares a video, Bytedance can
- tie the recipients of the video to the sender
- track recipients subsequently on Tiktok and Toutiao even if cookies are deleted.